Azure Single Sign-On for Web Client
Single Sign-On (SSO) adds more security and convenience when signing on to SEI using Azure Active Directory (Azure AD).
This topic describes how to set up Azure with SEI.
Configuring the Azure Domain
You must first configure the Azure Domain, as this is the platform from which we retrieve the data required to correctly set up SEI.
- In your Web browser, go to https://portal.azure.com/ and enter your login credentials (if required).
-
In the left menu, click Enterprise Applications.
-
In the upper bar, click + New application.
-
Under the Add your own app section, select Non-gallery application.
-
In the Name field, enter a name for your application and click Add.
-
Under the Getting Started section, select 2. Set up single sign on.
-
Select SAML for the single sign-on method.
Although there are 5 sections for the SAML SSO method, you only need to set the parameters in these sections:
Download the Azure Domain certificate from the SAML Signing Certificate section and use the Set up BI Web Server section as a reference for the mapping of terms from the SEI Installation Package. This is explained in further detail in Installing and Configuring the SEI Server.
Basic SAML Configuration
-
In the upper-right corner, click the pencil to edit the parameters in the Basic SAML Configuration section.
-
In the Identifier (Entity ID) field, enter your SEI URL + :port followed by a Unique Identifier for your Azure Domain. The URL and the port should be the same as those entered during the SEI installation.
ImportantOnly for users who never did the https binding for external access: Take note of URL address used for the Web Client on your certificate to communicate with the Azure Domain. This is explained in further detail in Installing and Configuring the SEI Server.
ExampleIn this example we have biwebserver.mycompany.com as the URL address with port :444 and biwebclient as Unique Identifier for the Azure Domain.
-
In the Reply URL (Assertion Consumer Service URL) field, enter your SEI URL + :port following by /AuthServices/Acs.
-
Click Save to apply changes.
-
In the left menu, under the Manage section, click Users and groups.
-
In the upper bar, click + Add user to authorize users and groups to use SSO.
This completes the basic SAML configuration.
User Attributes & Claims
The installation package for the configuration of the SEI application automatically fills in the SAML2 answer's Attribute for user name field with the mailnickname attribute by default.
For users installing the SEI Web Application for the first time: Please note that the screen above is explained in greater detail in Installing and Configuring the SEI Server.
For the Azure Domain, you can replace this value with one of the attributes listed in the User Attributes & Claims section.
If you want to use the mailnickname attribute (because you want to choose the part of the email address before the @ sign), you will have to create it, since this attribute does not exist by default in Azure Domain.
To create the attribute:
-
In the left menu, under the Manage section, click Single Sign-On.
-
In the upper-right corner, click the pencil to edit the User Attributes & Claims section.
- Click + Add new claim.
- In the Name field, enter mailnickname.
- For the Source, select Attribute.
- In the Source Attribute field, enter user.mailnickname.
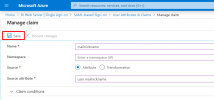
- Click Save to finish.
Installing and Configuring the SEI Server
Before starting the SEI Server Installation / Configuration, you must retrieve the certificate from Azure Domain.
To retrieve the certificate:
-
Scroll to the SAML Signing Certificate section.
-
Click Download next to the Certificate (Base64) field.
If SEI is already installed, go directly to Binding the Web Client. Otherwise, follow the procedure below.
For a First-Time Installation of SEI
- Follow the procedure described in Installing the Web Application and Distribution until Step 11.
-
In the App Configuration screen, fill in the fields as described below.
The mapping with SEI fields in the installation package is based on the Basic SAML Configuration and Set up BI Web Server sections in Azure Domain.
Field in SEI Installation Package = Field in Azure Domain Value used as example in this document SEI Issuer URI = Identifier (Entity ID) https://biwebserver.mycompany.com:444/biwebclient ID Provider Issuer Name = Azure AD Identifier https://sts.windows.net/c2c50f21-66a7-xxxx-xxxx-xxxxxxxxxxxx/ ID Provider URL = Azure Login URL https://login.microsoftonline.com/c2c50f21-66a7-xxxx-xxxx-xxxxxxxxxxxx/saml2 For the Full certificate name field, enter the name of the certificate you downloaded from Azure Domain with the .cer extension (for example: AzureBIWebServer.cer).
You should have a result similar to this:
-
Click Next and finish the installation.
Binding the Web Client
By adding an HTTPS binding to your Web Client, external connections will also be secured.
To bind the Web Client:
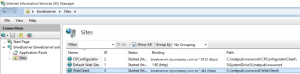
- Press the Windows key + R to open the Run window.
- Enter inetmgr and press the Enter key.
- On the left pane, click the little arrow to expand the connection tree structure.
- In the Sites tab, right-click on WebClient and select Edit Bindings...
- In the Site Bindings window, click Add...
-
In the Type drop-down list, select https. For this HTTPS connection, we are using port number 444 but you can customize it according to your preferences.
Editing the web.config file
In order to fully benefit from Azure SSO functionality, you will have to edit the web.config file located in C:\inetpub\wwwroot\WebClient.
- Make sure the entityID attribute from the sustainsys.saml2 tag has the same value you defined in the Identifier (Entity ID) field in the basic SAML configuration. In our example we set "https://biwebserver.mycompany.com:444/biwebclient" as value.
- Change the other values in the SEI web.config file as described in the table below:
| Attribute to be changed in the web.config file | Value before change | Value after change | Comment |
|---|---|---|---|
| returnUrl | "http://biwebserver.mycompany.com:444/Account/SSO" | "https://biwebserver.mycompany.com:444/Account/SSO" | We added an s to http since we want this connection to be secured. |
| entityID from the identityProviders tag | "https://stubidp.sustainsys.com/Metadata" | "https://sts.windows.net/c2c50f21-66a7-xxxx-xxxx-xxxxxxxxxxxx/" | This is the value you retrieved from the Azure AD Identifier field in the Set up BI Web Server section |
| signOnUrl from the identityProviders tag | "https://stubidp.sustainsys.com/" | "https://login.microsoftonline.com/c2c50f21-66a7-xxxx-xxxx-xxxxxxxxxxxx/saml2" | This is the value you retrieved from the Azure Login URL field in the Set up BI Web Server section |
Web Browsers have updated their policy regarding cookies and these changes must be applied to your Web Client if you want SEI embedded into your ERP website, or use Single Sign-On (SSO). Refer to Cookie Management for more details.
| Attribute to be changed in SEI web.config file | Value before change | Value after change |
|---|---|---|
| cookieSameSite | |
|
| httpOnlyCookies / requireSSL / sameSite | |
|
Expected result for the Web Client
<sustainsys.saml2 entityId="https://biwebserver.mycompany.com:444/biwebclient" returnUrl="https://biwebserver.mycompany.com:444/Account/SSO" modulePath="/AuthServices">
<identityProviders>
<add entityId="https://sts.windows.net/c2c50f21-66a7-xxxx-xxxx-xxxxxxxxxxxx/" signOnUrl="https://login.microsoftonline.com/c2c50f21-66a7-xxxx-xxxx-xxxxxxxxxxxx/saml2" allowUnsolicitedAuthnResponse="true" binding="HttpRedirect">
<signingCertificate fileName="~/App_Data/AzureBIWebServer.cer"/>
</add>
</identityProviders>
</sustainsys.saml2>Expected result for the cookies
<system.web>
<sessionState cookieSameSite="None"/>
<compilation targetFramework="4.8">
<assemblies>
<add assembly="System.Core, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089"/>
</assemblies>
</compilation>
<!-- change value of MaxHttpCollectionKeys to max int(2147483644) to webserver support recsive big data-->
<httpRuntime targetFramework="4.8" maxUrlLength="10999" maxRequestLength="2147483644" executionTimeout="1600" useFullyQualifiedRedirectUrl="false" requestLengthDiskThreshold="2147483647" maxQueryStringLength="2097151"/>
<httpCookies httpOnlyCookies="true" requireSSL="true" sameSite="None"/>
</system.web>Steps after the Installation/Configuration
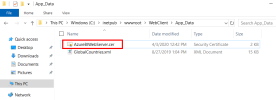
Copying the Azure Domain Certificate
-
Copy the certificate you downloaded from Azure Domain and paste it to C:\inetpub\wwwroot\WebClient\App_Data.
Creating Users and Groups in SEI
- Refer to Users to create your Web Client user by entering the same value for User Name and SAML2 answer's Attribute for user name you defined during the installation of the package.
Accessing SEI with Azure SSO enabled
To log in with SSO enabled, use your default Web Client URL:
https://biwebserver.mycompany.com:444
If your Admin account is not set up with SSO and you need to log in, use this URL to log in with your default credentials (without SSO):
https://biwebserver.mycompany.com:444/Account/Login